Data security controls
Overview of data security controls
Types of data collected
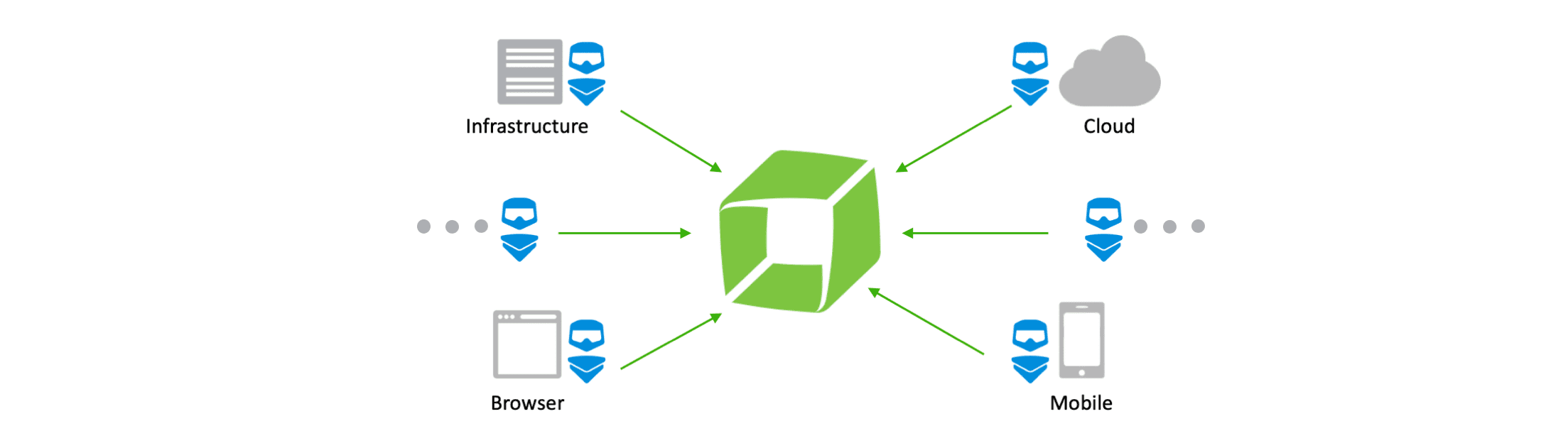
Dynatrace can capture various types of infrastructure and application data, including host and application metrics, basic network metrics, real user metrics, mobile metrics, cloud infrastructure metrics, log metrics, and much more.
By default, Dynatrace doesn't collect personally identifiable information (PII). However, since Dynatrace can be configured to capture PII, we also provide you with robust data masking and data protection features. These features are designed to help you comply with your data privacy and data protection obligations.
Data storage
Data is stored in Amazon Web Services (AWS), Microsoft Azure, or Google Cloud data centers. The available regions are listed below.
AWS regions
Available on request. Talk to your Dynatrace sales contact.
Azure regions1
East US (Virginia)
West US 3 (Arizona)
West Europe (Netherlands)
Canada Central (Toronto)
UAE (Dubai)
Switzerland North (Zurich)
Available on request. Talk to your Dynatrace sales contact.
Google Cloud regions1
us-east4 (N. Virginia)
europe-west3 (Frankfurt)
Available on request. Talk to your Dynatrace sales contact.
Also see Data retention periods.
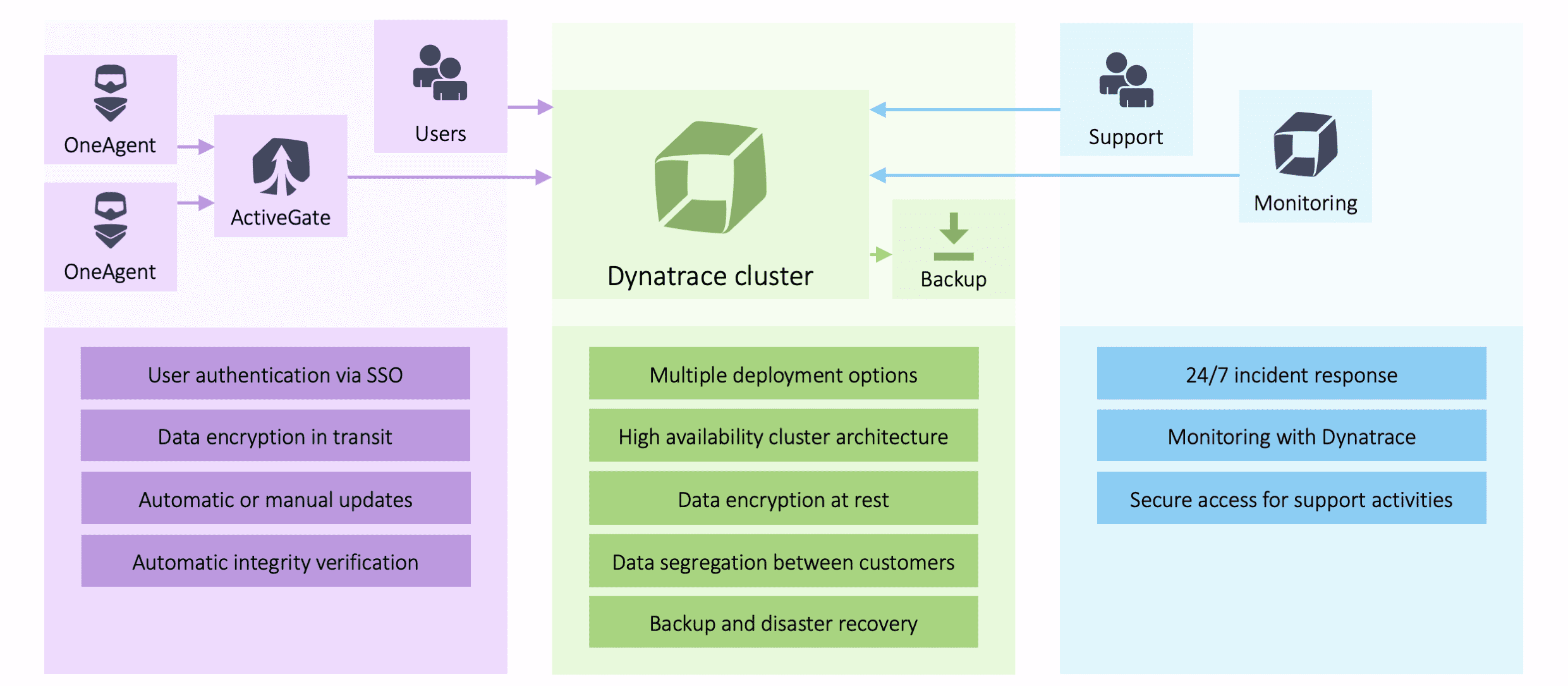
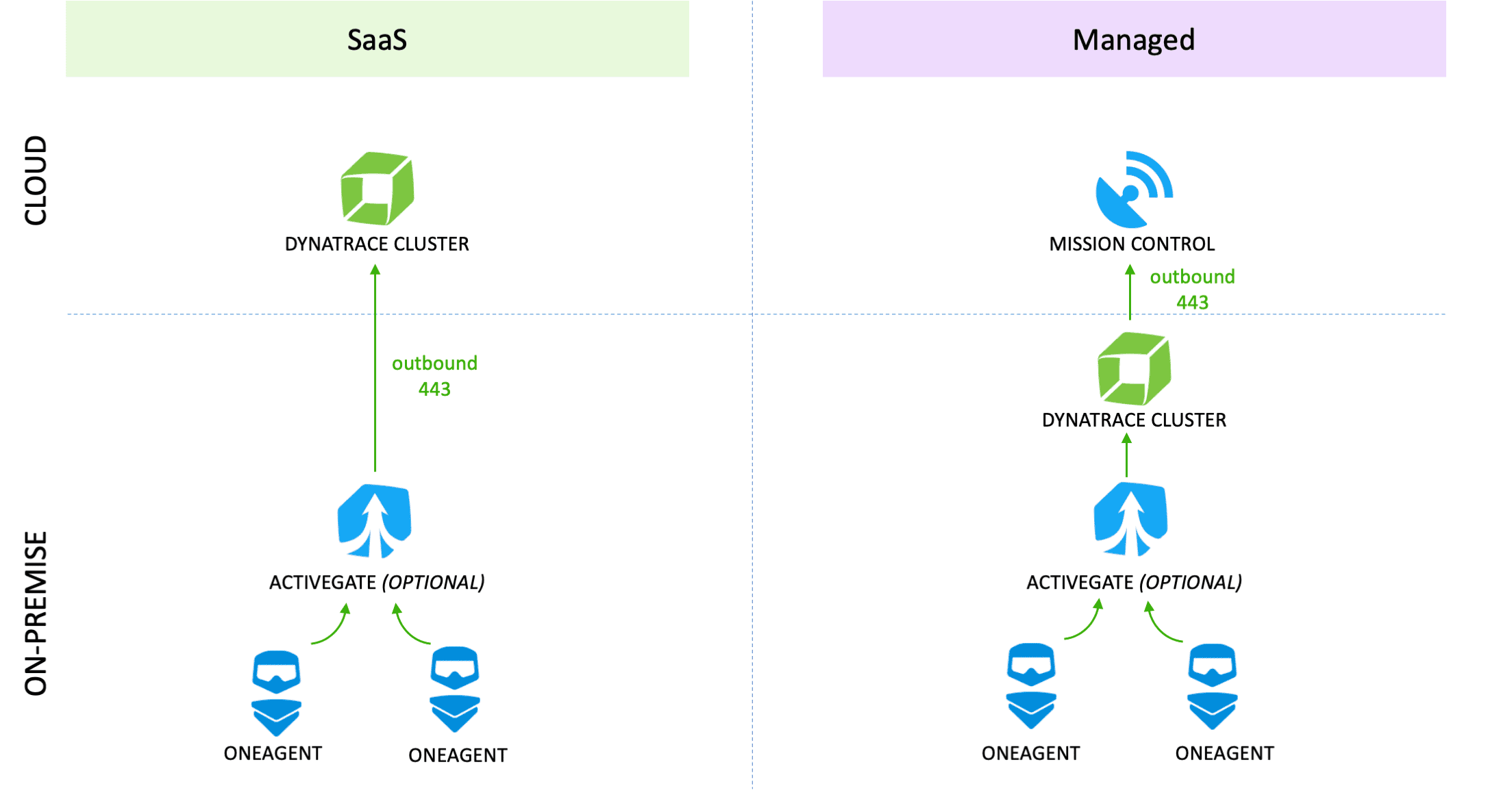
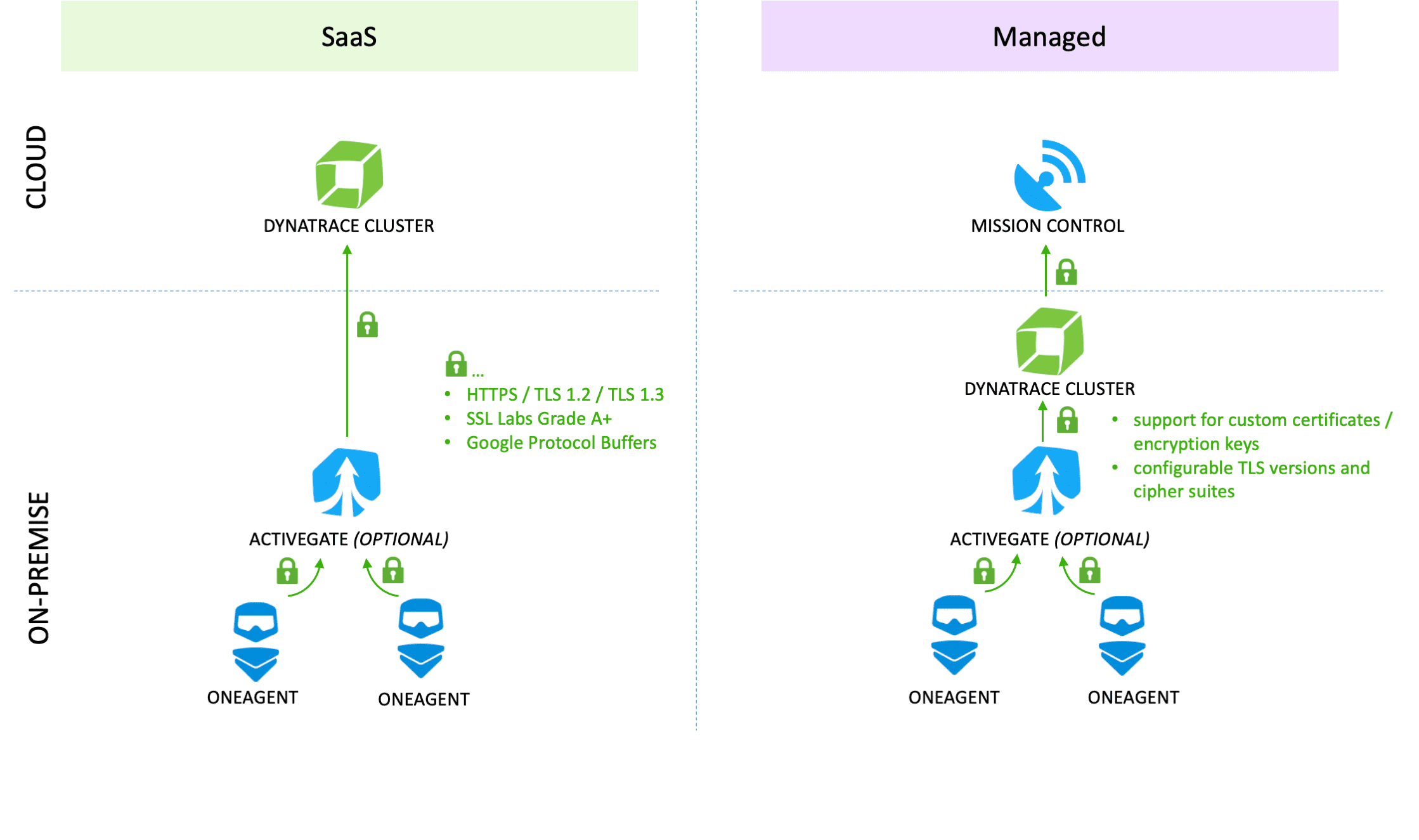
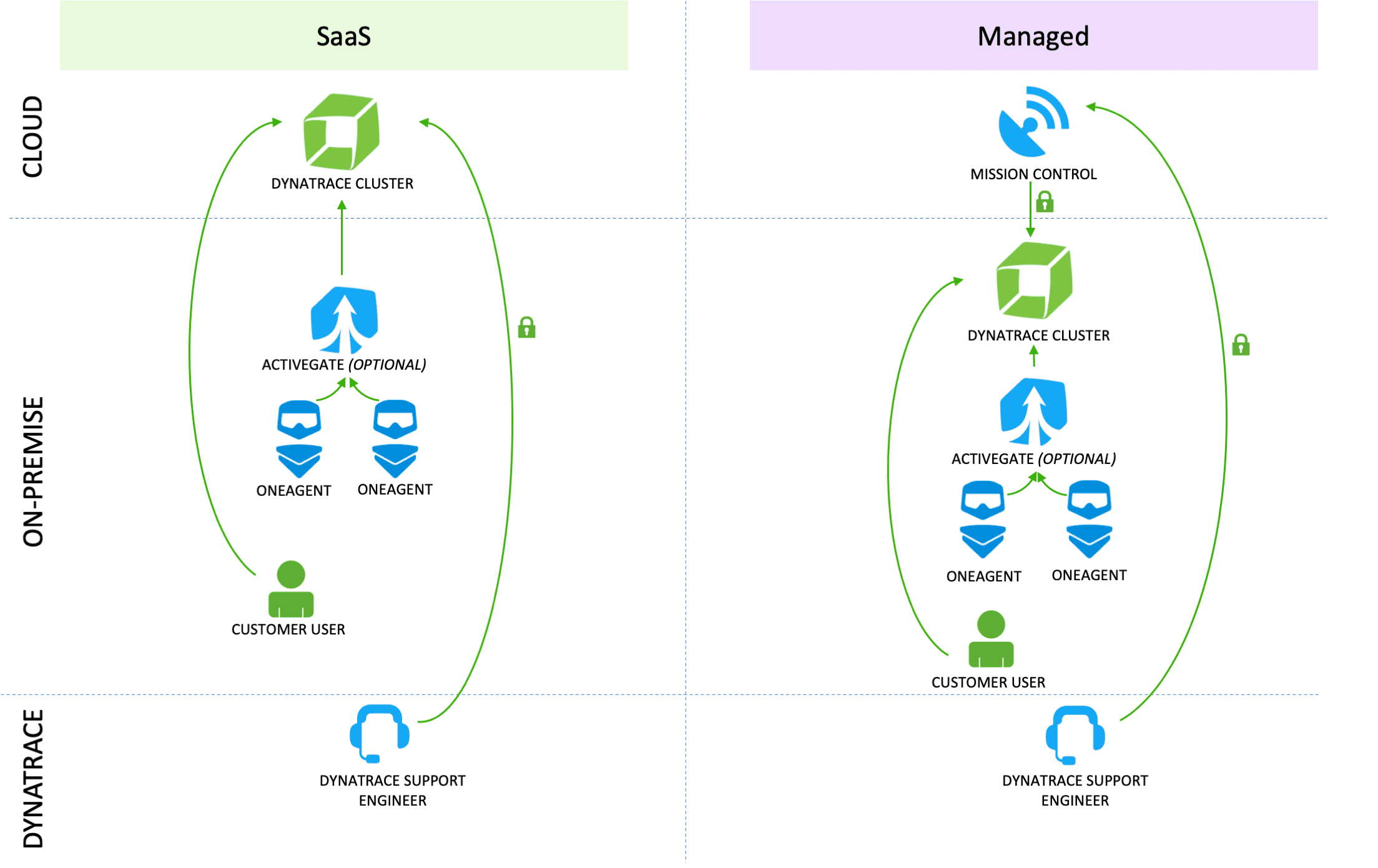
Dynatrace components
Dynatrace OneAgent collects all monitoring data within your monitored environment. Optionally, all data collected by OneAgent can be routed through a Dynatrace ActiveGate, which works as a proxy between Dynatrace OneAgent and the Dynatrace Cluster. In the absence of an ActiveGate, data collected by OneAgent is sent directly to the Dynatrace Cluster.
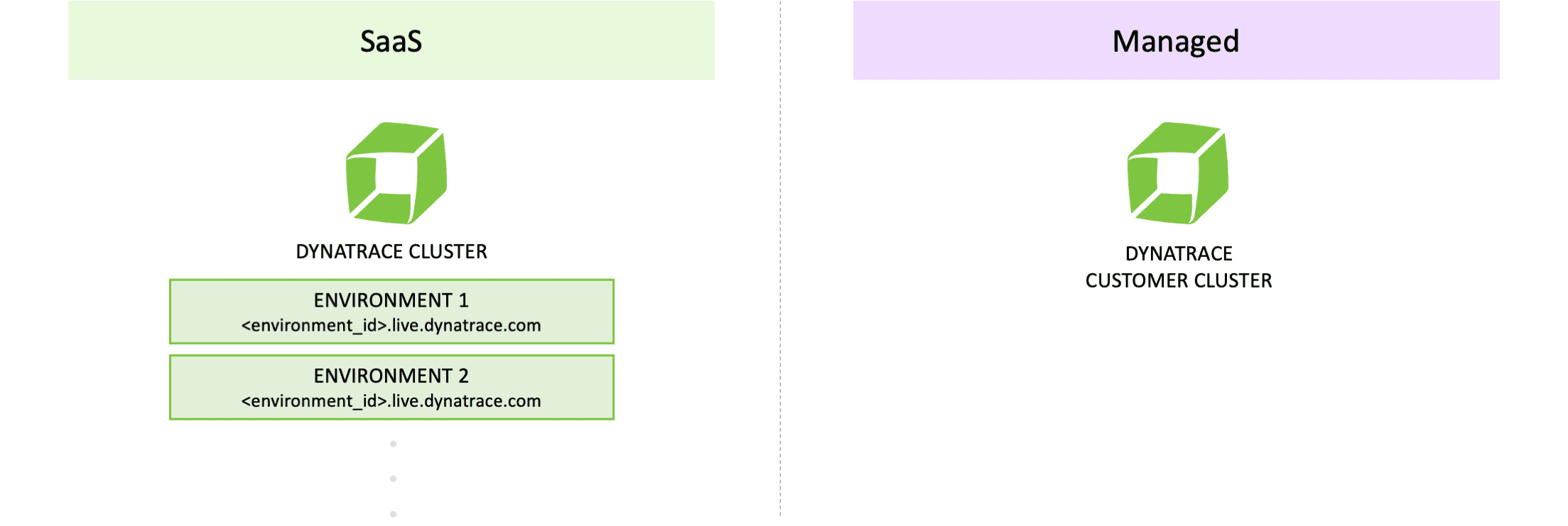
Data segregation between customer environments
Dynatrace SaaS allocates one dedicated environment per customer account. Data is segregated logically and each environment gets its own individual domain.
Data encryption in transit
All data exchanged between OneAgent, ActiveGate, and Dynatrace Cluster is encrypted in transit. Data is serialized and deserialized using Google Protocol Buffers.
Dynatrace SaaS supports TLS 1.2 and TLS 1.3 (SSL Labs Grade A+).
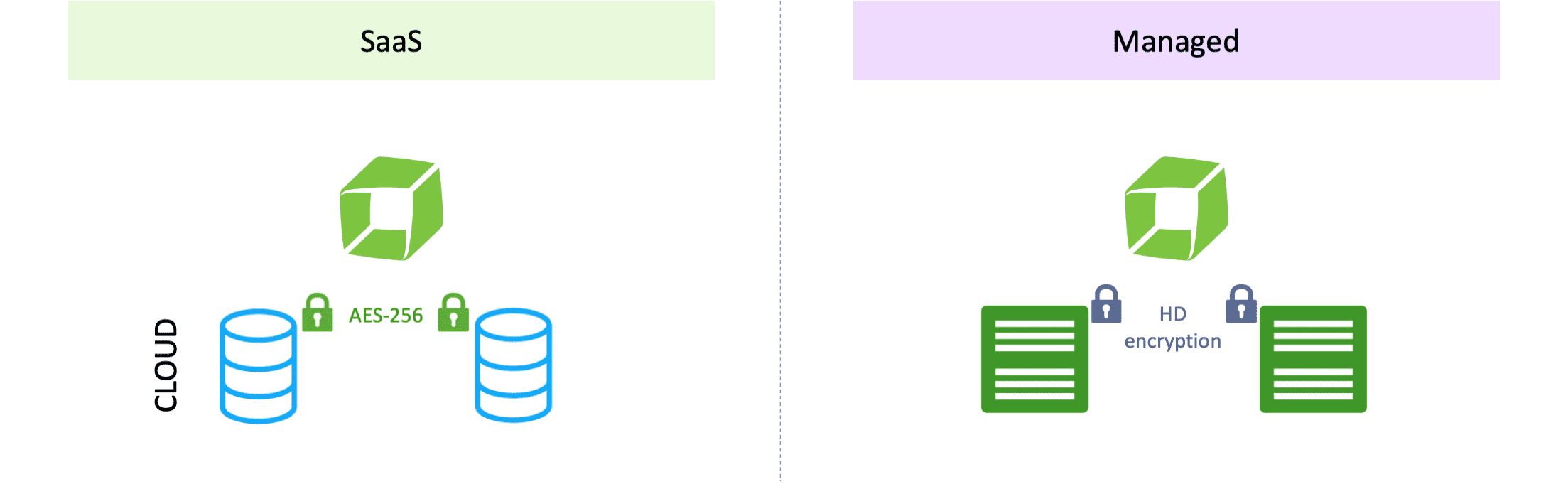
Data encryption at rest
AWS. Dynatrace SaaS on AWS uses Amazon Elastic File System (EFS) and Amazon Elastic Block Store (EBS) with AES-256 encryption. Dynatrace manages encryption keys using AWS Key Management Service (KMS).
Azure. Dynatrace SaaS on Azure uses Azure Storage with Microsoft-managed keys. Data in Azure Storage is encrypted and decrypted transparently using AES-256 encryption (FIPS 140-2 compliant).
Google Cloud. Dynatrace SaaS on Google Cloud uses persistent disks with keys managed by Google Cloud. Google Cloud encrypts all customer content stored at rest with 256-bit AES encryption and uses a FIPS 140-2 validated Level 1 encryption module (certificate 3318).
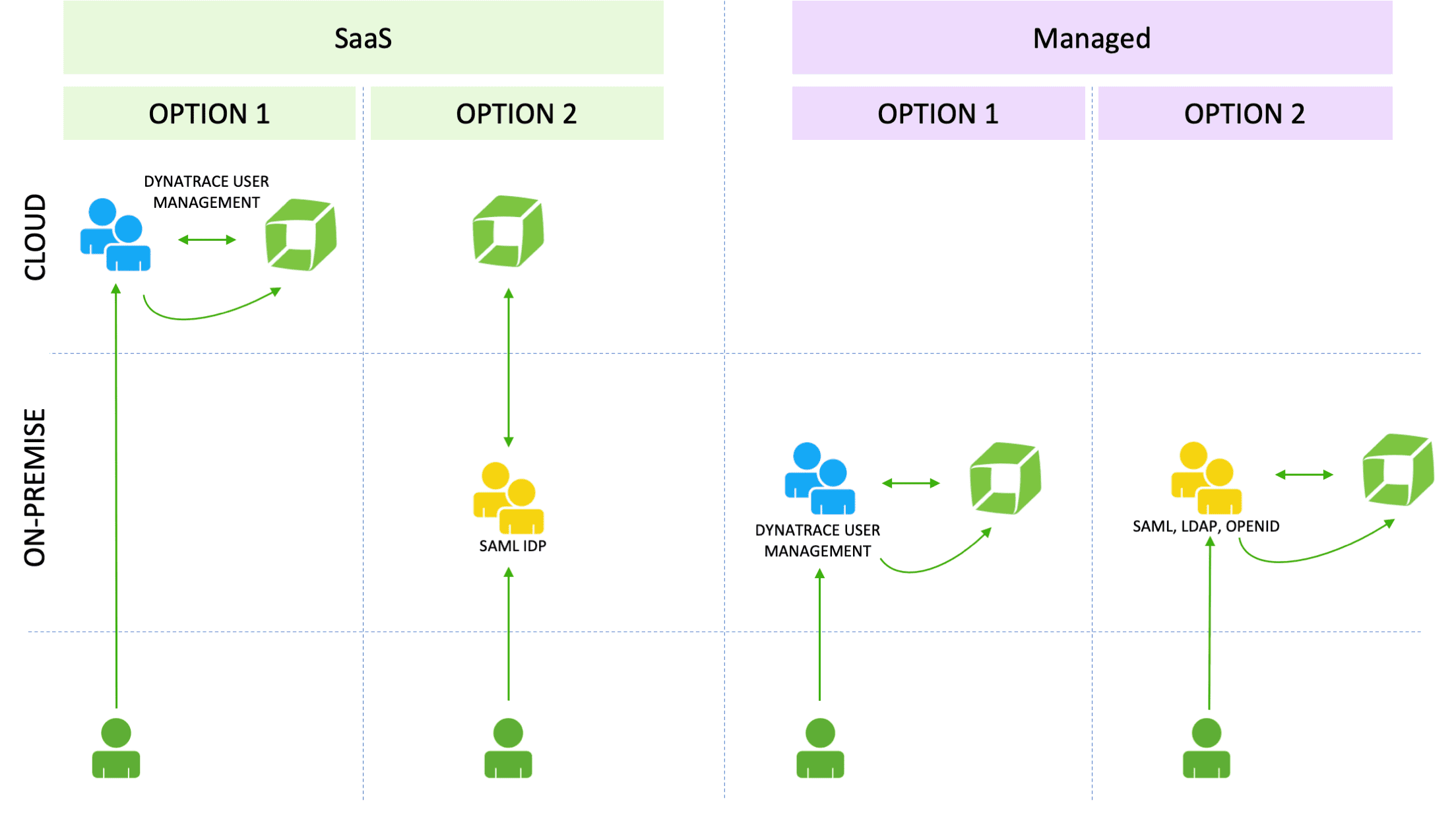
User authentication
You can manage your users by setting up user groups and permissions and SAML.
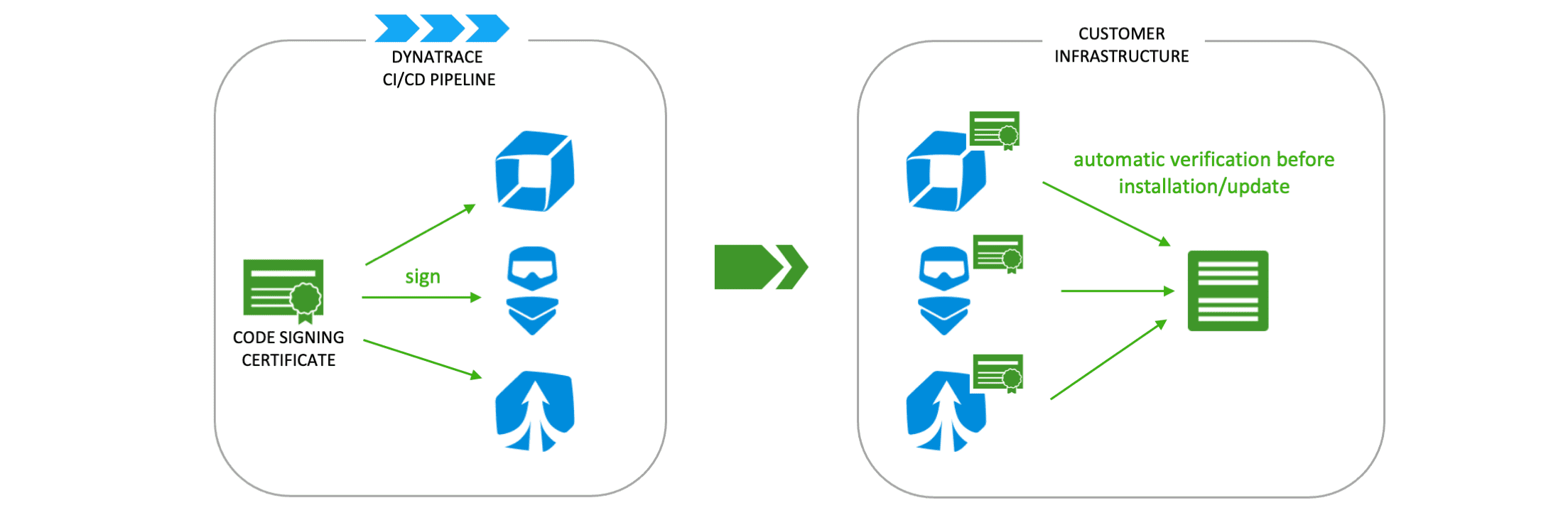
Integrity verification of Dynatrace components
Dynatrace components are signed using code signing certificates within the continuous delivery and integration (CI/CD) pipeline.
Code signing certificates are stored on hardware tokens with Extended Validation (EV) code signing certificates for Windows. Signature verification is performed automatically before an update or installation. When installing a component for the first time, signature verification must be conducted manually.
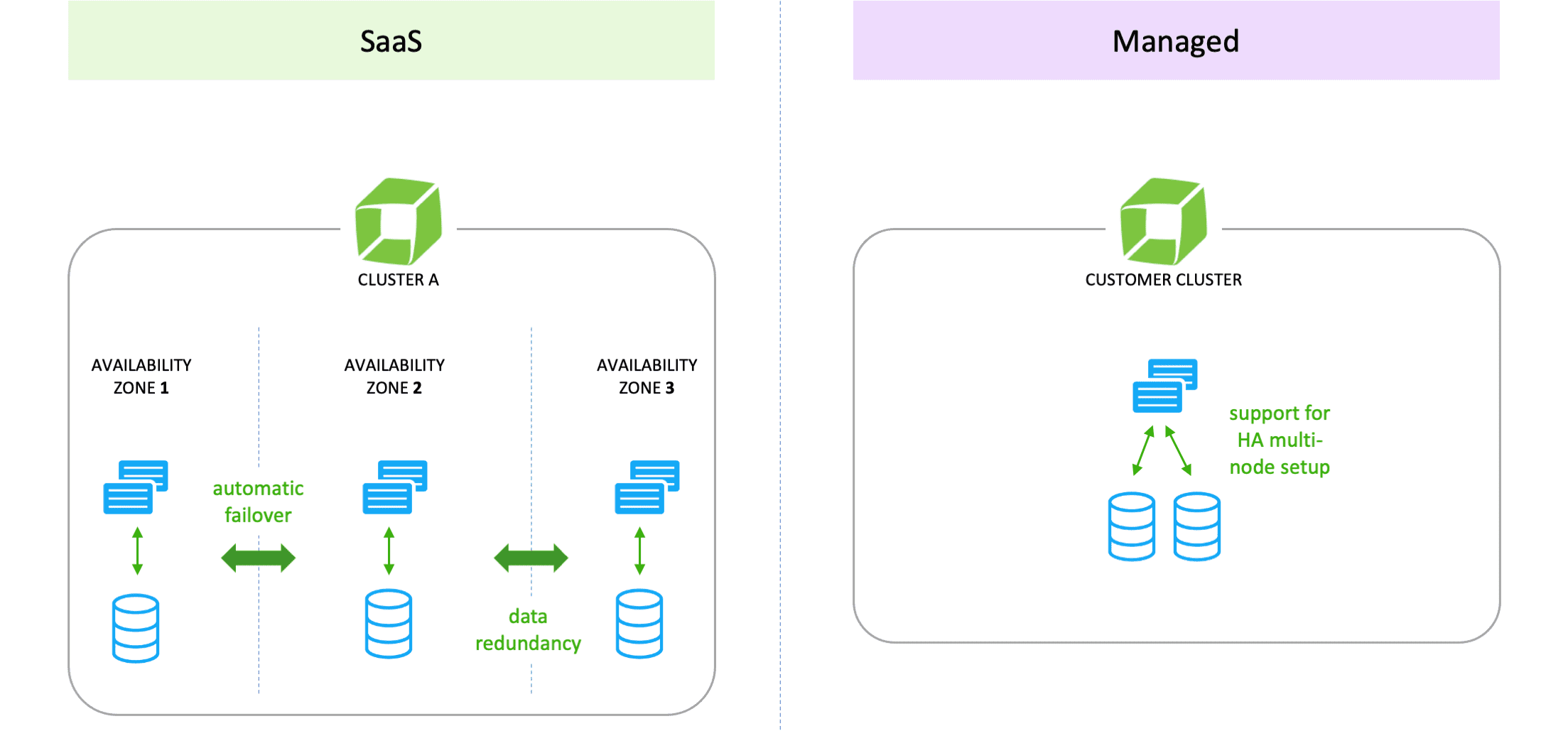
Business continuity and high-availability
Dynatrace SaaS uses a clustered architecture, multiple availability zones (data centers), and automatic fail-over mechanisms to ensure high availability (99.5% availability SLA).
Data backups and disaster recovery
-
AWS: Every 24 hours, Dynatrace SaaS on AWS performs data backups to a different AWS account in the same AWS region. The backup includes the data captured for at least the last 30 days. The maximum recovery point objective (RPO) for a full cluster is 24 hours. The recovery time objective (RTO) takes up to 24 hours, depending on the size of the cluster.
-
Azure: Every 24 hours, Dynatrace SaaS on Azure performs data backups to a different Azure subscription in the same Azure region. The backup includes the data captured for at least the last 30 days. The maximum recovery point objective (RPO) for a full cluster is 24 hours. The recovery time objective (RTO) takes up to 24 hours, depending on the size of the cluster.
-
Google Cloud: Every 24 hours, Dynatrace SaaS on Google Cloud performs data backups to a different Google Cloud project in the same Google Cloud region. The backup includes the data captured for at least the last 30 days. The maximum recovery point objective (RPO) for a full cluster is 24 hours. The recovery time objective (RTO) takes up to 24 hours, depending on the size of the cluster.

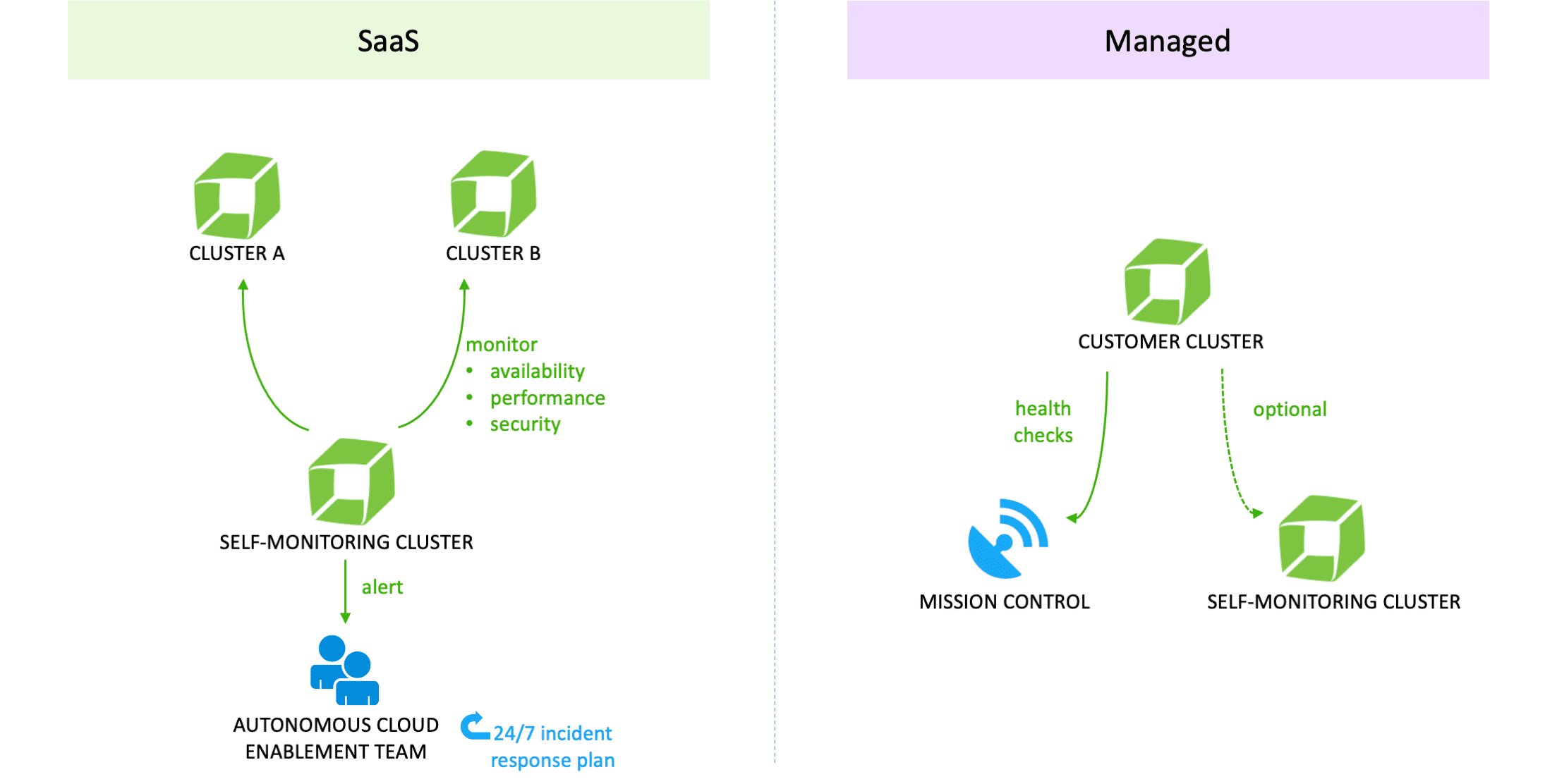
Infrastructure monitoring
A dedicated Dynatrace self-monitoring cluster monitors availability, performance, and security of all SaaS clusters. If a problem is detected, the Dynatrace ACE (Autonomous Cloud Enablement) team, which operates on a 24/7 basis, is notified immediately. Operational status and incidents are always available at dynatrace.status.io.
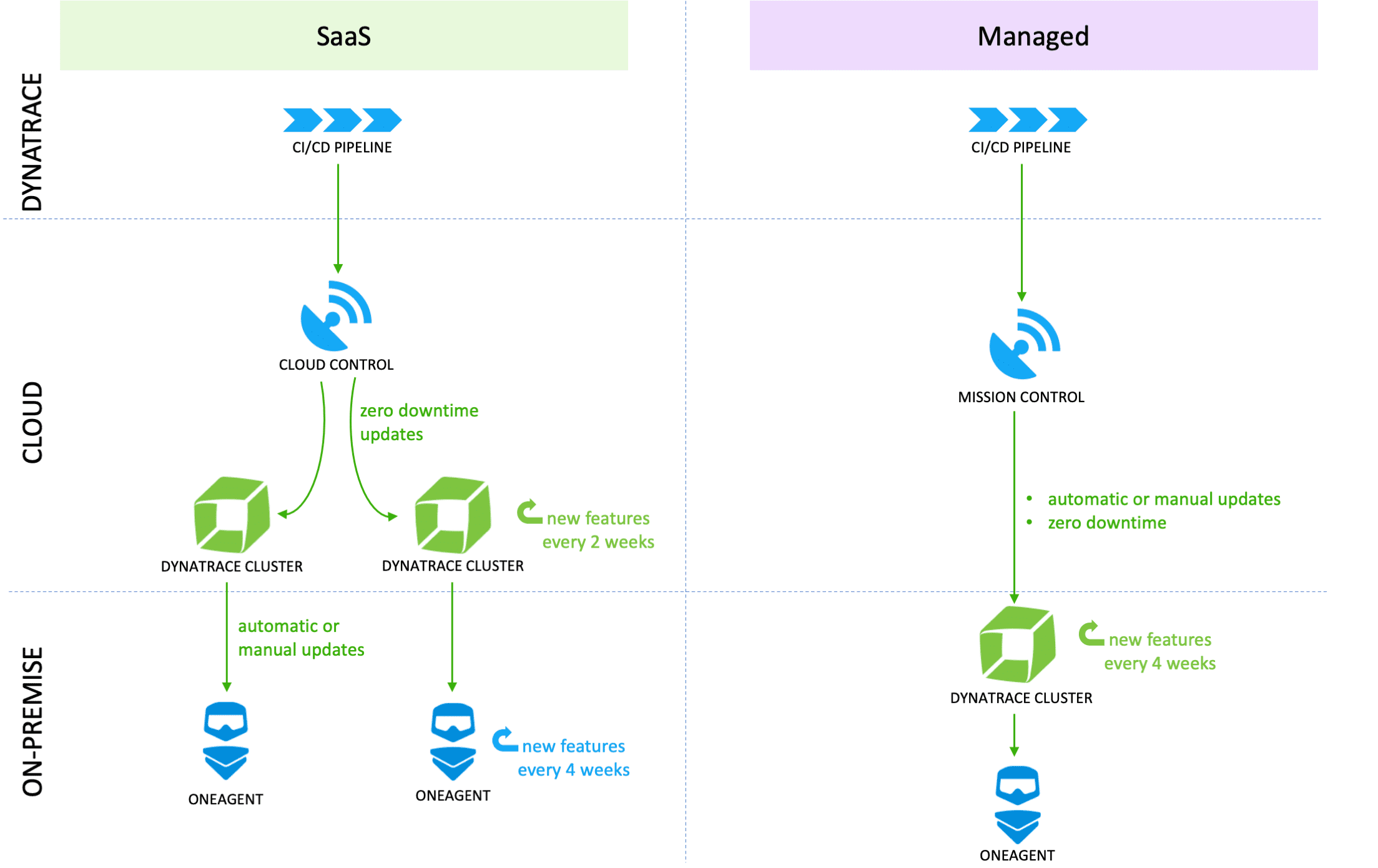
Roll out of updates and hot fixes
Using a fully automated CI/CD pipeline, Dynatrace is able to roll out updates and hot fixes within a few hours. The Dynatrace architecture allows for zero-downtime upgrades of clusters.
New features are delivered every two weeks. Updates of Dynatrace ActiveGates and OneAgents can be performed automatically or manually.
Data access for Dynatrace support
Access to Dynatrace SaaS environments is role-based. Role changes require justification and approval by the Dynatrace ACE (Autonomous Cloud Enablement) team. Access is restricted to the Dynatrace corporate network and requires multi-factor authentication when accessed remotely. Every access and all changes are audit logged and fully accessible.
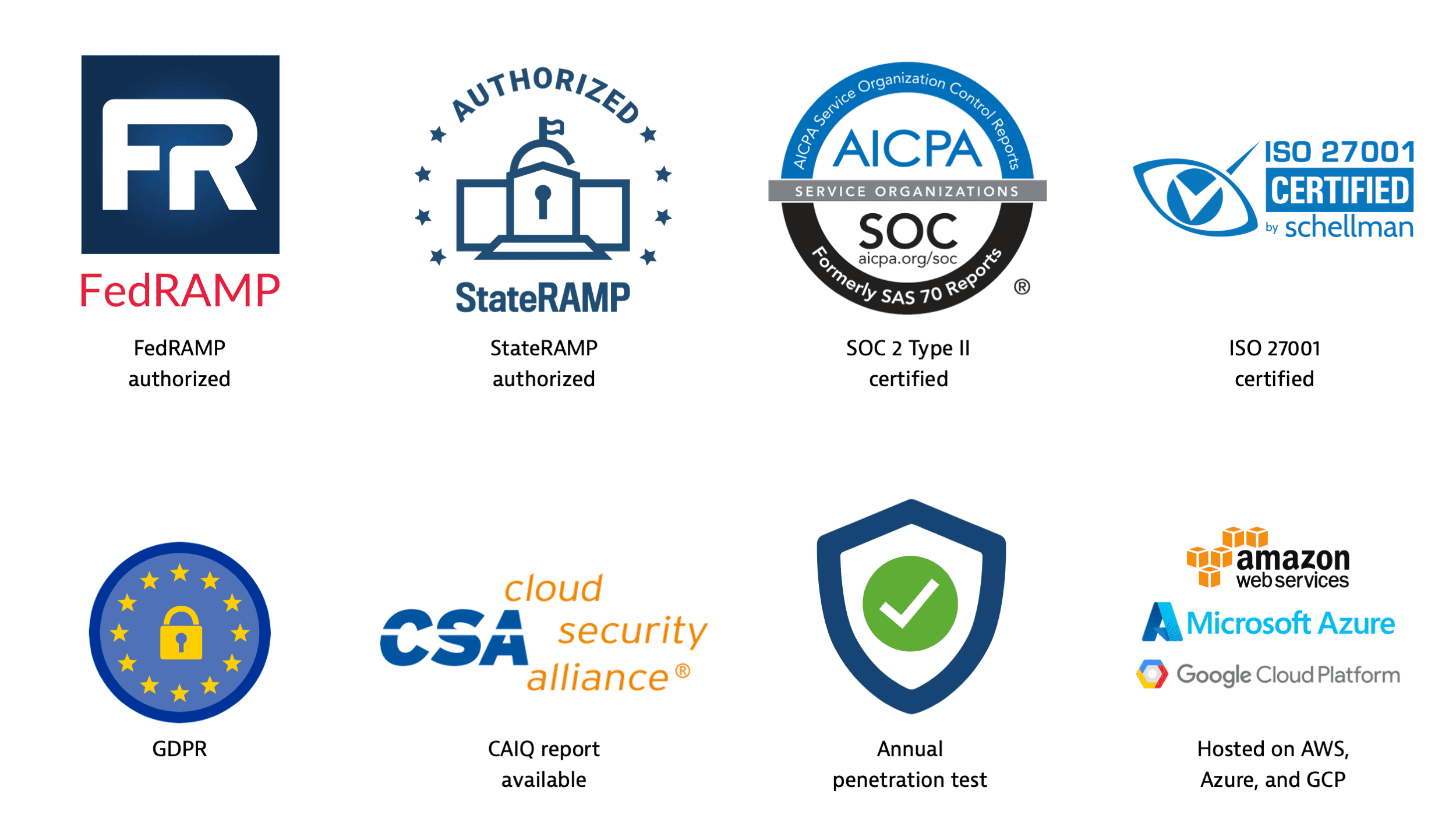
Compliance, certifications, and audits
Dynatrace undergoes annual, independent third-party SOC 2 Type II audits. You can view the SOC 3 report, but the full SOC 2 report is available only under an NDA. Dynatrace can be used in a GDPR-compliant way (Europe), performs regular self-assessments (see Cloud Security Alliance CAIQ report), and conducts penetration tests with independent security firms.
Additionally, Dynatrace offers a deployment option that is both FedRAMP-authorized and StateRAMP-authorized at the Moderate baseline security level.
You can enable the FIPS mode to ensure OneAgent is compliant with the FIPS 140-3 computer security standard.
Dynatrace has achieved ISO 27001 certification for our Information Security Management Systems (ISMS), covering Dynatrace SaaS, Dynatrace Managed, and all associated applications and technologies that are hosted, developed, and maintained by Dynatrace. This certification demonstrates that we adhere to the most recognized international standard for security management, which is focused around our product, product infrastructure, and IT environment.
Dynatrace also benefits from secure Amazon, Azure, and Google data centers that are certified for ISO 27001, PCI-DSS Level 1, and SOC 1/SSAE-16.