IBM MQ tracing
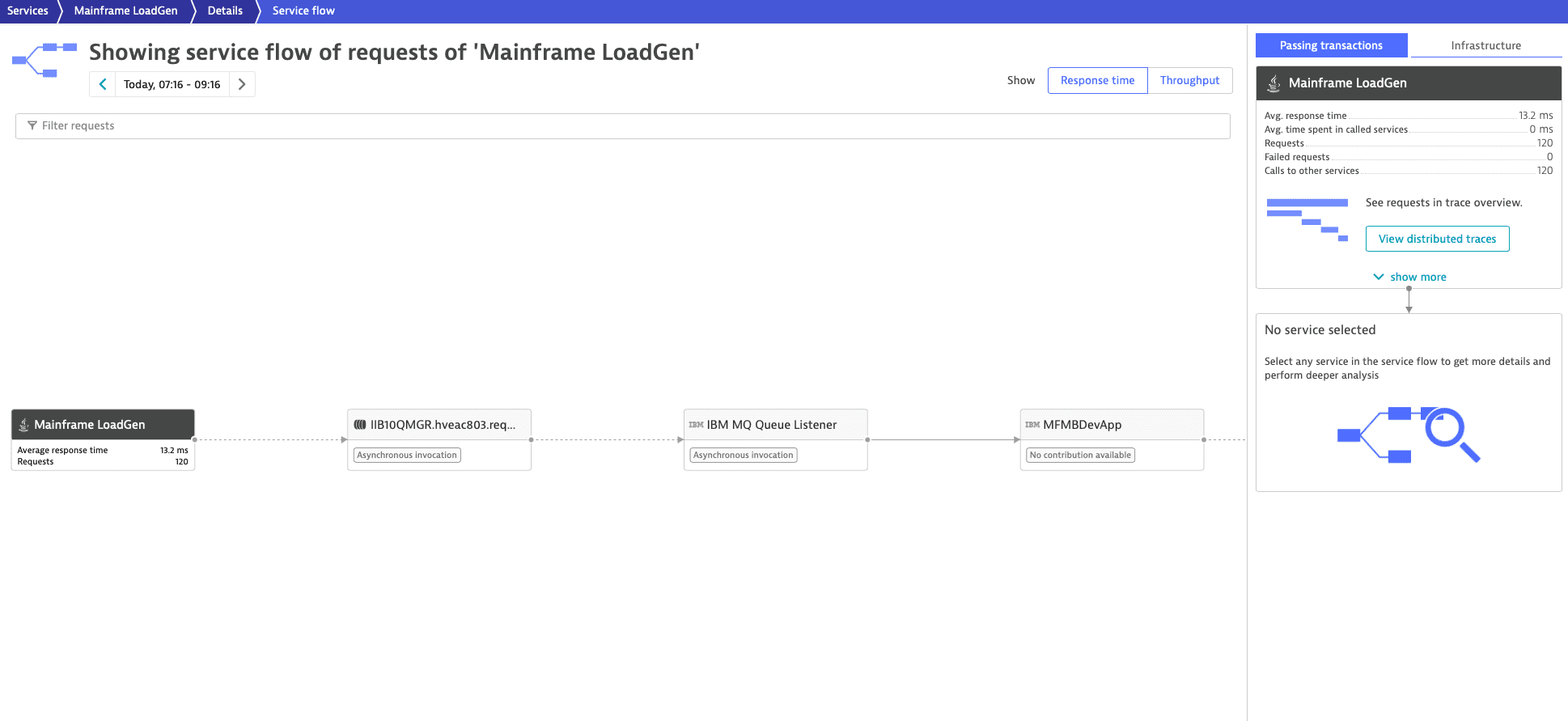
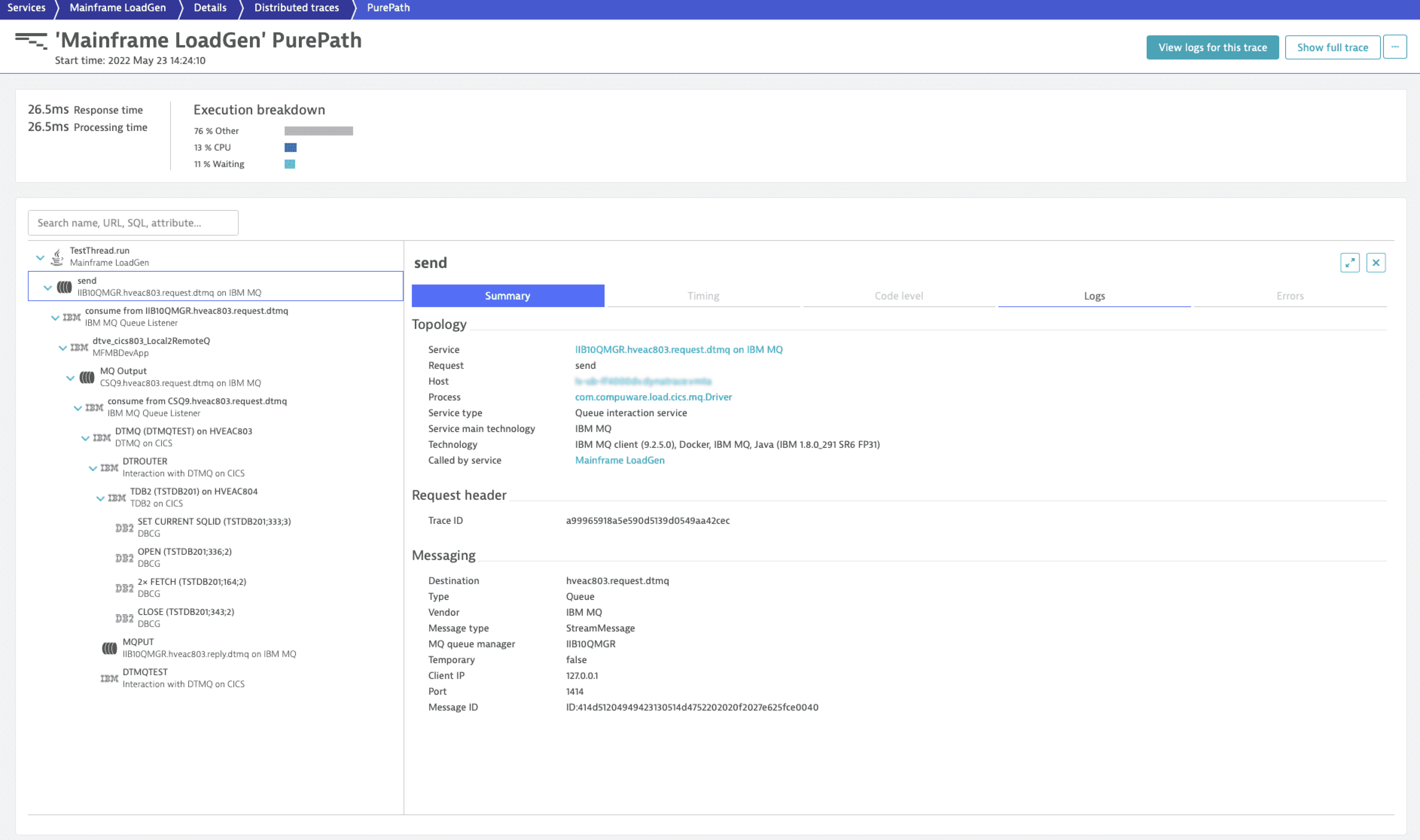
Dynatrace can automatically create a continuous service flow for IBM MQ when the producer and consumer services use the same queue or topic name. If the producer and consumer services refer to different queue or topic names, IBM MQ configuration might be required to create a continuous service flow.
Without IBM MQ configuration, Dynatrace can still trace all messages, but the service flow will be broken.
| Technology | IBM MQ message | IBM MQ configuration required |
|---|---|---|
z/OS Java .NET | ||
IBM App Connect EnterpriseIBM Integration Bus |
|
Frequently asked questions
We recommend that you create the MQRFH2 header for IBM MQ messages. The presence of the MQRFH2 header in your IBM MQ messages allows Dynatrace to use identifiers instead of unique keys to trace messages across queues and topics of IBM App Connect Enterprise and IBM Integration Bus.
Benefits of creating the MQRFH2 header for IBM MQ messages include:
- Consistent Adaptive traffic management across your monitoring environment, lowering the volume on IBM MQ traces.
An accurate and continuous service flow without the need to configure IBM MQ mapping when the messages are solely processed by IBM App Connect Enterprise and IBM Integration Bus.
When the MQRFH2 header is present in your messages before an MQOutput node is called by IBM App Connect Enterprise or IBM Integration Bus, Dynatrace uses identifiers instead of unique keys to trace IBM MQ messages.
If this isn't the case in your environment, you can create an empty MQRFH2 header by, for example, executing the following ESQL command by a preceding Compute node
CREATE LASTCHILD of OutputRoot DOMAIN 'MQRFH2';
For Dynatrace, an empty MQRFH2 header is enough to automatically create the usr folder and to add Dynatrace identifiers to it. If a usr folder is already present, Dynatrace reuses it.
- Dynatrace creates the
usrfolder within the existingMQRFH2header, not theMQRFH2header itself. - When creating the
usrfolder, Dynatrace adds it at the beginning of theMQRFH2header. - If the
usrfolder exists, Dynatrace adds its identifiers at the beginning of theusrfolder.
Manage IBM MQ configuration
You can manage an IBM MQ configuration automatically by installing an IBM MQ extension and activating Retrieve topology for improved transaction tracing to retrieve the IBM MQ configuration of your environment and send it to the Settings API. This can also be done manually via the web UI or the Settings API.
Manual configuration via web UI
To manage the IBM MQ configuration via the Dynatrace web UI, go to Settings > Mainframe to find the following menu options:
IBM MQ queue managers
IBM MQ queue sharing groups
IBM MQ IMS bridges
Manual configuration via Settings API
You can manage the IBM MQ configuration via the Dynatrace Settings API.
To be able to use the API you need an access token with Read settings (settings.read) and Write settings (settings.write) scopes. To learn how to obtain it, see Create an access token.
Configuration items
The table lists the available IBM MQ configuration items for queues and topics.
| Item | Description | Your action |
|---|---|---|
Queue manager | Queue manager with its queues | Define your queue managers, including alias queues, remote queues, and cluster queues within a single configuration item. |
z/OS Queue sharing group | Group of queue managers that access the same shared queues | Specify which queue managers and shared queues belong to a queue-sharing group within a single configuration item. |
z/OS IMS bridge | The IBM MQ component that allows direct access to the IMS system | Specify which queue managers and queues belong to an IMS bridge within a single configuration item. |
Follow the procedures below to create or update a configuration item. Note that the scope of these items is always an environment. Before starting, learn the format of the settings object by querying its schema via the GET a schema call.