Observability for financial services
Deliver resilient, secure, and compliant digital experiences across banking, payments, and insurance with AI-powered observability.
Observability built for the demands of financial services
Dynatrace helps financial institutions modernize safely, ensure uptime, meet regulatory demands, and protect customer trust at scale.
Put observability to work across financial services
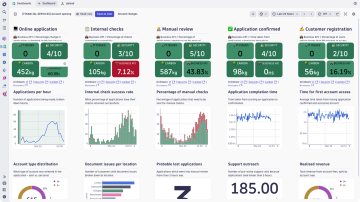
Protect always-on banking, payments, and core financial services
- Monitor end‑to‑end customer transactions across core banking, payments, and lending processes
- Detect performance anomalies across mainframe, cloud, and third‑party services
- Understand the customer and business impact of issues during peak transaction periods
- Prioritize and resolve incidents based on risk to revenue, customer trust, and service levels
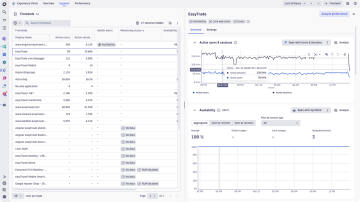
Optimize digital banking experiences
- Monitor real-user experience across mobile and online banking applications
- Identify friction and drop-offs in critical journeys like login, payment, and servicing
- Correlate backend performance with frontend experience in real time
- Improve customer satisfaction while reducing support costs
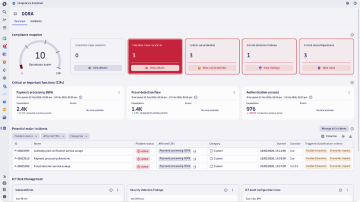
Support compliance and risk management
- Map compliance‑relevant IT assets to critical business processes to align IT, legal, and business teams
- Monitor real‑time compliance health and deviations across critical processes with framework‑specific views
- Detect and classify potential major incidents in real time, aligned to regulatory impact thresholds
- Streamline audit readiness and regulatory reporting with tailored, framework‑specific insights