Transparency and traceability of configuration changes are key to enabling multiple teams to collaborate effectively. Audit logs are crucial for tracking changes and security-relevant events. Until now, audit logs were only available to Dynatrace Managed customers.
We’re happy to announce that with the release of Dynatrace 1.183, audit logs are now available for Dynatrace SaaS customers. In keeping with our API-first approach, the logs are accessible via REST API.
With the new environment Audit logs API, Dynatrace SaaS and Managed customers can track changes to configurations, see who made a specific change, or what a certain configurable value was before a change. It’s also a great feature for security and compliance, as it makes login events, logout events, as well as changes to API tokens accessible.
Access audit logs via the new REST API endpoint
You can access or download the audit logs of a given SaaS or Managed environment via a new REST API endpoint. This endpoint returns audit events in JSON format. So you have the highest flexibility in processing the audit events, ingesting them into any other system, or just viewing the well-structured output in a text editor.
Which events are logged?
You can access logs of the following events from the audit logs:
- Login events
- Logout events
- Any change to a configuration
- Any change to API tokens
What properties does an audit event have?
Each audit event has the following properties:
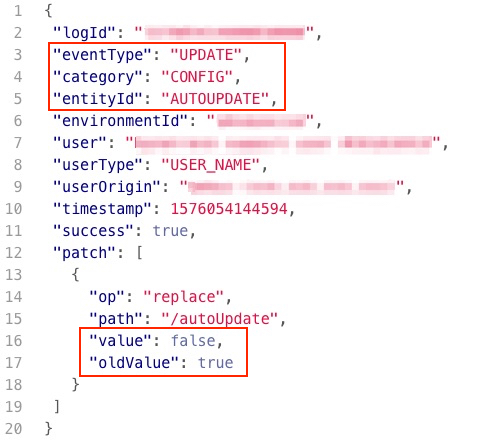
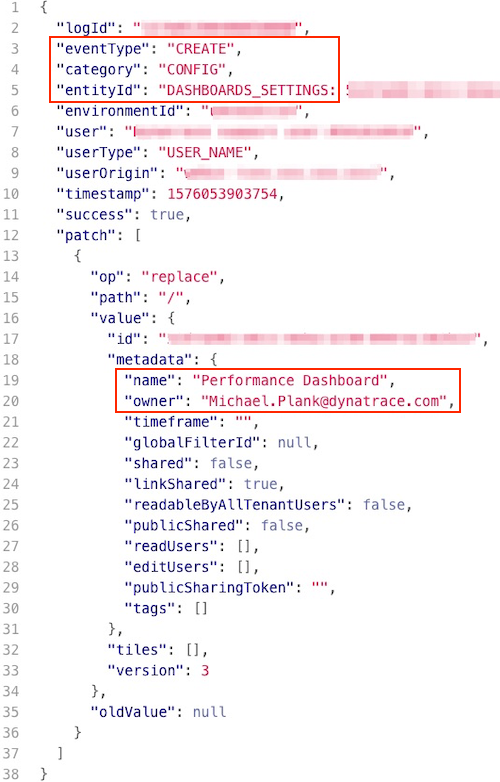
logId: A unique ID for each log eventeventType: The event type (for example,LOGIN,LOGOUT,CREATE,UPDATE, orDELETE)category: The change category (for example,CONFIG;TOKENorWEB_UIin case of a login/logout)entityId: The entity that was changed (DASHBOARDS_SETTINGS,SUB_ENVIRONMENT,AUTOUPDATE, and others)environmentId: The environment IDuser: The email address of the user who triggered the eventuserType: The user type (for example,USER_NAMEif a person made the change,SERVICE_NAMEif a built-in mechanism made the change)userOrigin: The origin of the user who triggered the event (for examplewebui,system)timestamp: When the event was triggered (UNIX timestamp format)success: Whether the event was executed successfullypatch(optional): Includes values before and after a change
Example 1: Audit event showing that the OneAgent AutoUpdate was turned off
Example 2: Audit event showing that a new dashboard called “Performance Dashboard” was created
See only events you’re interested in by filtering the output
The great thing about making audit logs available via a REST API is that you can filter the output to view only events of interest. Here are a few examples:
- Get only login events:
filter=eventType(LOGIN) - Get all configuration changes in the last two hours:
filter=category(CONFIG) from=now-2h - Get only changes to API tokens:
filter=eventType(UPDATE),category(TOKEN)
How to set up audit logging
Prerequisite: User must have environment admin permissions.
To enable and use the new environment Audit logs API
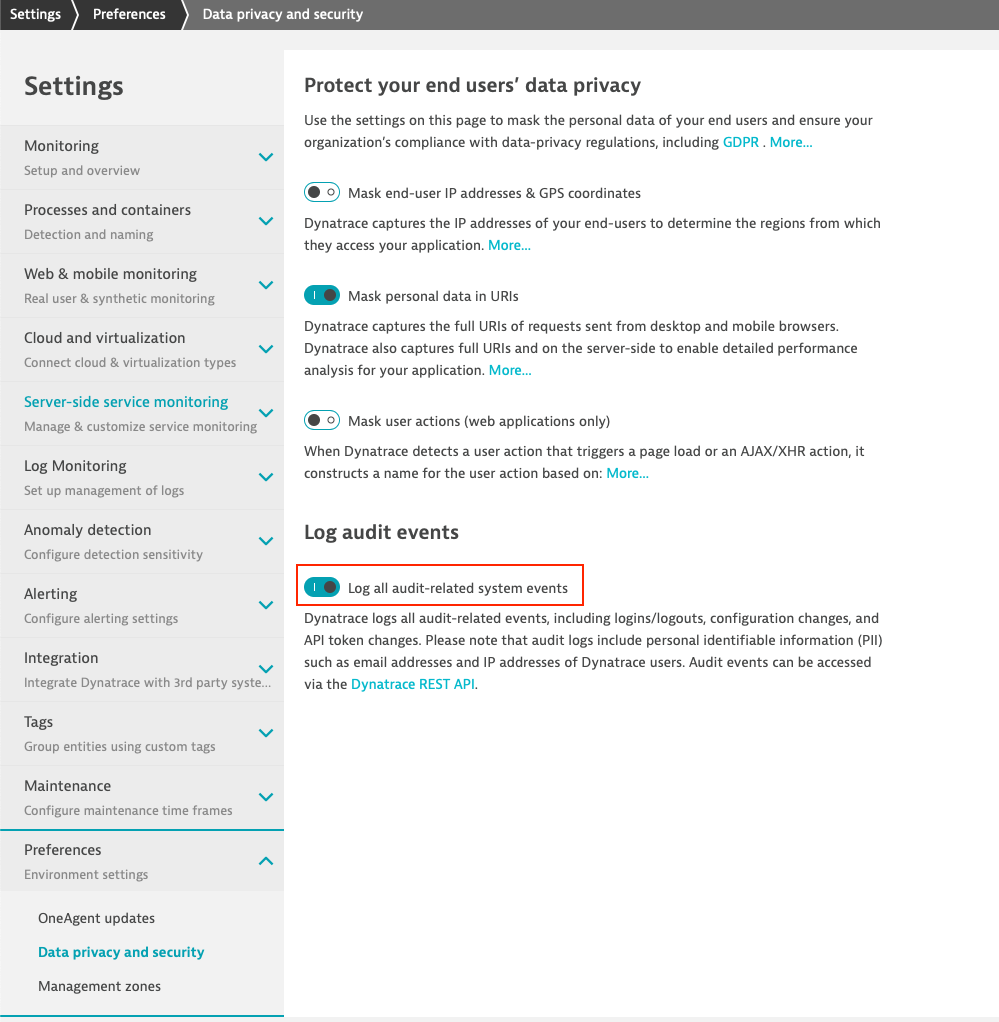
- Go to Settings > Preferences > Data privacy and security and enable Log all audit-related system events.
- Go to Settings > Integration > Dynatrace API > Generate token. Give the token a name and enable Read audit logs. Alternatively, use an existing API token by adding this access scope.
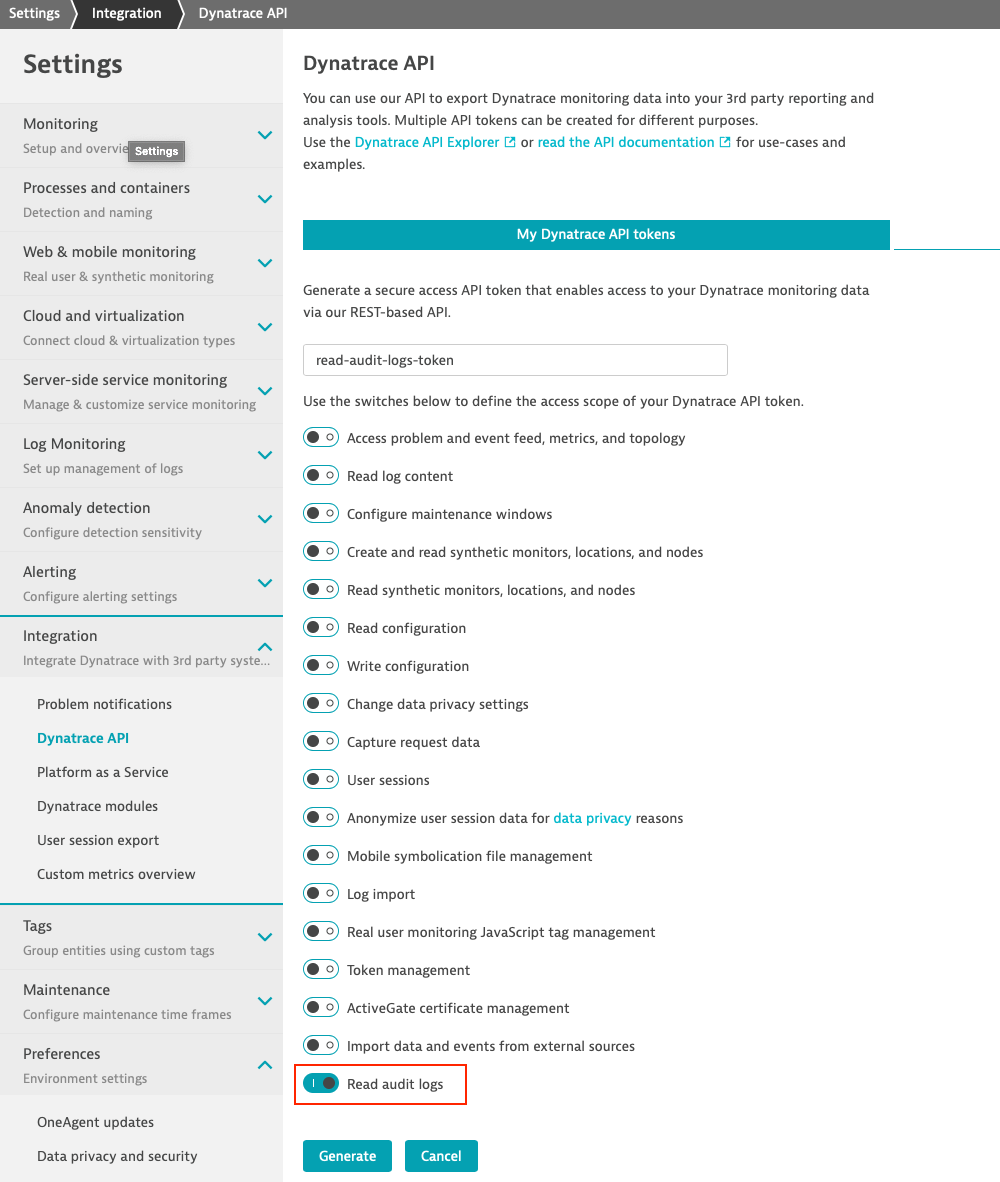
- Copy the Generated token value.
- The
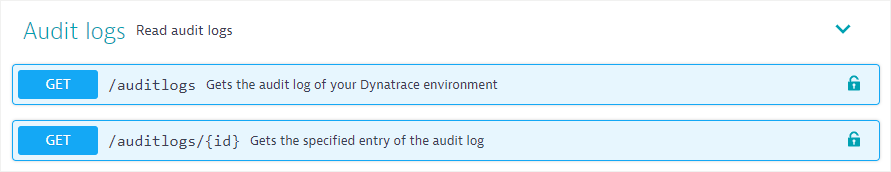
/auditlogsAPI endpoint is available in the Dynatrace Environment API v2.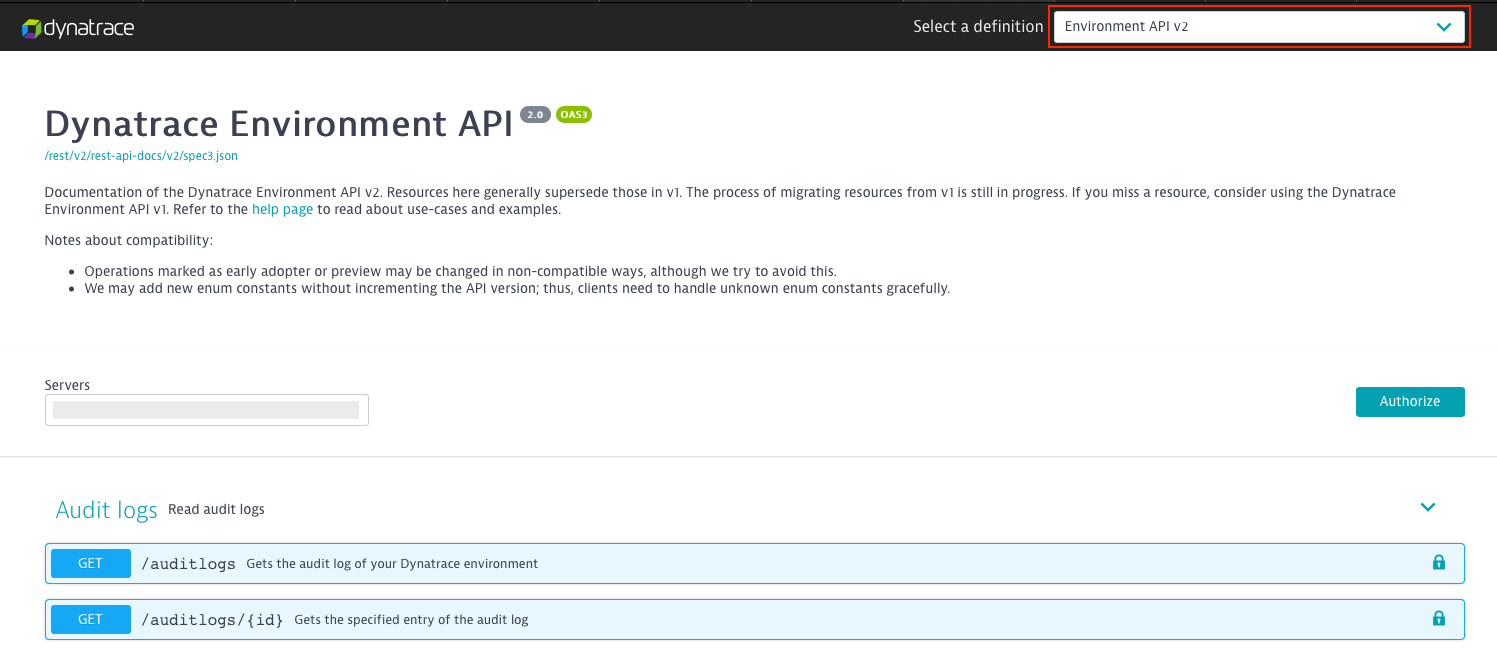
- Use the copied API token within the
Authorizationheader to get the audit logs for a given timeframe.
Audit log retention
Environment audit logs are stored once the audit feature is enabled, as explained in the first step of the setup above. Events that occur before the feature is enabled aren’t stored!
Audit logs are retained for 30 days and then automatically deleted.
Note: If you need to store audit logs for a longer period of time, for example, to meet compliance standards, we recommend that you set up an automated process that downloads audit logs every day and stores them in your own infrastructure.
What’s next?
This is the first version of the new environment Audit logs API. We’re looking forward to your feedback regarding how you make use of this new functionality, along with any ideas for improving it. Please post your feedback, questions, or improvement requests in our user forum. Tell us what you love about audit logs, or what we can do better!





Looking for answers?
Start a new discussion or ask for help in our Q&A forum.
Go to forum