With role-based governance for large global teams, automatic enterprise-wide deployment and full-stack coverage across infrastructure, cloud platforms, and applications, Dynatrace is made for the most demanding enterprise environments. At our largest customers we see hundreds of users working together in Dynatrace from around the globe. In order to scale, such enterprises need the ability to quickly and securely add or remove user accounts, change permissions, or add new types of accounts.
Until now, group access management in Dynatrace SaaS, like adding and removing groups, had to be done manually via the Dynatrace web UI, either for local entities or for SAML.
In addition to the UI based user management approach, today we’re happy to announce that from now on you can automatically provide your Dynatrace SaaS environments with user- and group identity information from your organization’s identity provider (IdP) through SCIM 2.0 (System for Cross-domain Identity Management).
Do more with less by easily provisioning user access via SCIM 2.0 (Early Adopter)
SCIM is an open standard for automating the exchange of user- and group identity information between identity domains or IT systems. It makes user data more secure and simplifies the user experience by automating the user identity life-cycle management process.
With this enhancement you’ll be able to create and maintain users and groups in your Dynatrace SaaS environments by provisioning resources directly from your organization in a secure way. This means that when a user is deactivated or removed, or a user’s access has been limited (for example, if they’ve been removed from account admin roles), other account admins don’t have to remember to remove the user or limit user access manually in the Dynatrace web UI. This is done immediately in the next provision cycle after you make the change in a system that is integrated with Dynatrace.
Since SCIM is an open standard, user data is stored in a consistent way and can be communicated as such across different apps. Thus, IT departments will be able to automate the provisioning/deprovisioning process while also having a single system to manage resources.
What if SAML is already in use?
If the domain is verified in SAML, the domain will be considered verified for SCIM.
Also, if SAML authorization has already been set up in your account, SCIM can take over the burden of manual group mappings. Once you’ve completely switched over to SCIM you can disable SAML authorization and remove SAML groups forever. Or you can start working with SCIM simultaneously with the current SAML authorization setup. SAML and SCIM groups will then work independently and all user groups permissions will be joined together.
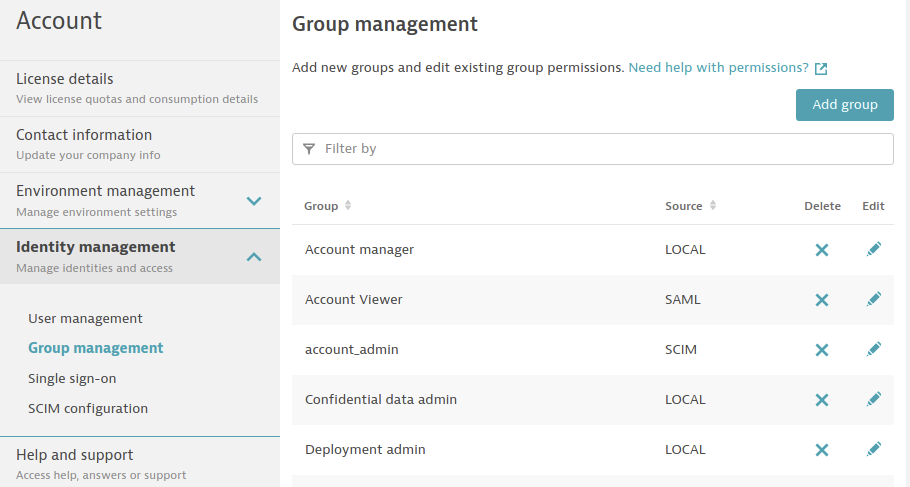
Within BAS, go to Account > Identity management > Group management. The Source types are LOCAL, SAML or SCIM. Note that SCIM groups can’t be renamed or transformed to SAML or LOCAL.
Requirements and supported features
Dynatrace supports SCIM 2.0, which includes GET, POST, PATCH, PUT, DELETE operations for both User and Group resources.
For authentication SCIM requires a Bearer token in the Authorization header.
The userName attribute is required to be in email format. User email needs to be persistent (email changes are not supported).
Dynatrace SCIM requires and supports four SCIM attributes:
userNamename.givenNamename.familyNameactive
Dynatrace SCIM doesn’t support password synchronization due to security concerns. Usually SCIM integration goes hand in hand with SAML authentication that is done on your organization IdP side—then no further action is required by the new user. If SAML isn’t enabled in your account then the newly created user needs to set the password on the Dynatrace side before logging in for the first time using the Forgot your password? option.
The Early Adopter version of SCIM support requires that each group have a unique name.
SCIM configuration
SCIM configuration on the Dynatrace side is easy.
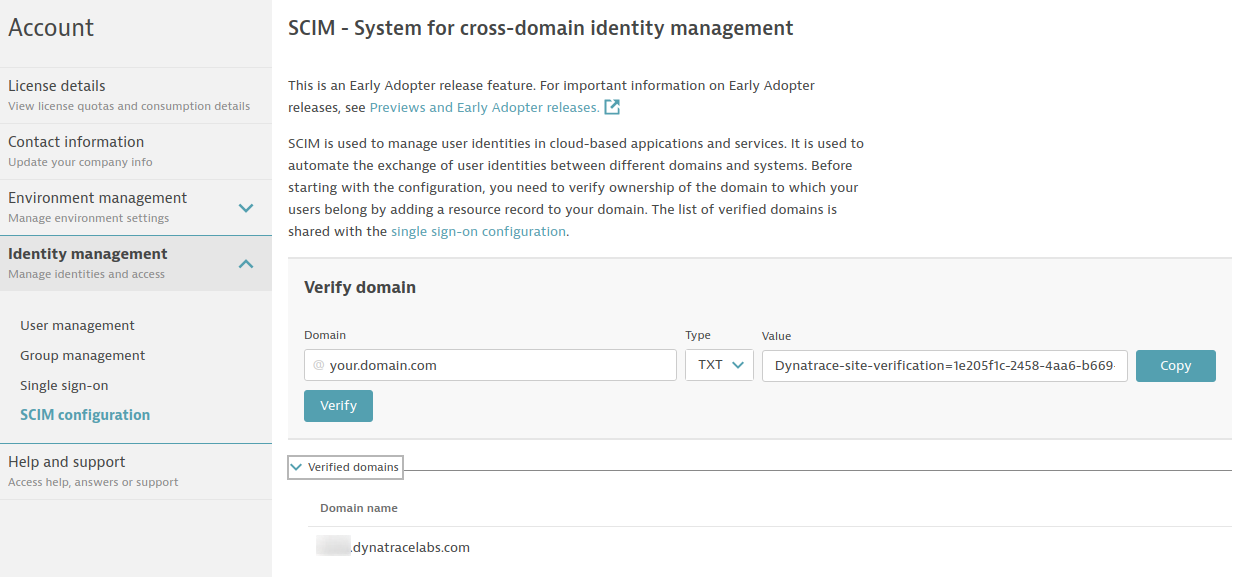
- Verify domain (only required if you haven’t yet completed SAML authorization configuration)
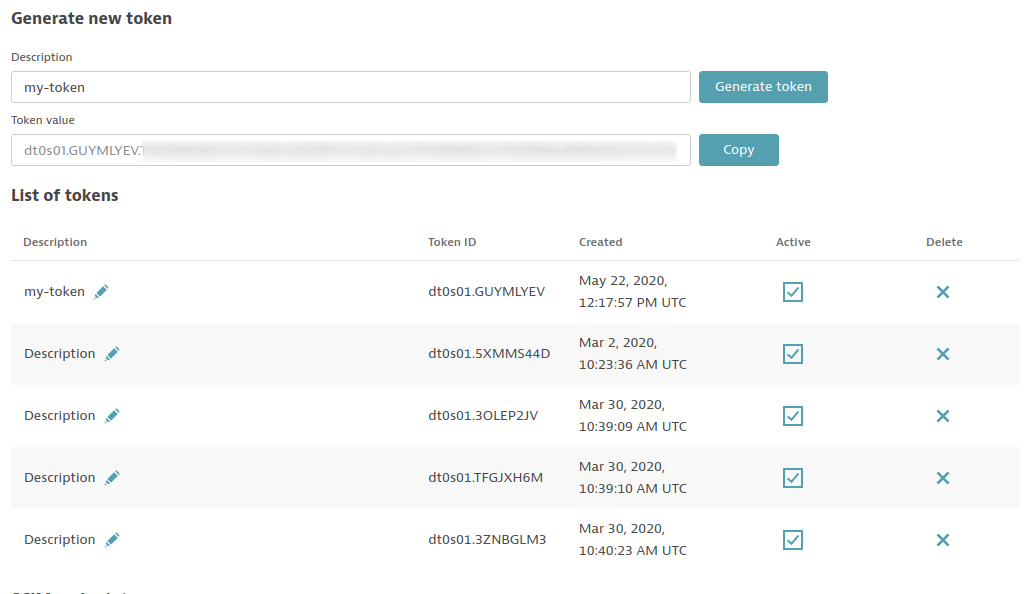
- Generate SCIM token
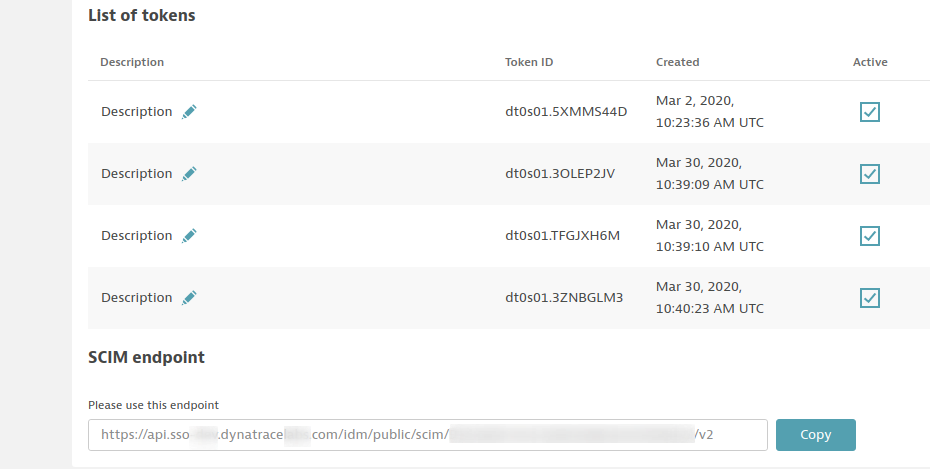
- Copy SCIM endpoint
Domain verification
Domain verification proves your ownership of the domain and allows you to provision users with emails from this domain in Dynatrace.
You can verify multiple domains in the single account.
To verify a domain, in the Verify domain section on SCIM configuration page:
- Enter your domain
- Copy the TXT value
- Add new TXT resource record with copied value to your domain’s DNS configuration
- Select Verify
It typically takes a few minutes for a record to propagate through the DNS system and the value to become available for Dynatrace to verify. In some cases, it may take up to 24 hours.
After successful verification, the domain is listed in the Verified domains list.
SCIM token generation
In the Generate new token section, select Generate token. You may want to add a short description for the token that explains its usage. The description can easily be added later.
Keep in mind that the token is revealed only once when it’s generated. You need to copy and paste the token to a secure location at that time. If you lose it, you have to generate a new token and replace it in your application.
There can be at most 10 tokens generated. Once you reach this number, you need to delete a token before you can generate a new token.
SCIM base endpoint
The SCIM base endpoint is generated automatically and is unique per account. The SCIM endpoint is listed beneath your token list.
With the SCIM token and the SCIM base endpoint you are fully equipped for Dynatrace SCIM integration in your SCIM client.
What’s next
We’re currently working on integrating our SCIM solution with the most popular identity providers (either as an enhancement to Dynatrace or as a dedicated SCIM application) like Azure or Okta. Stay tuned and watch for the new functionalities in your IdP Dynatrace applications.
We want to hear your feedback
As always, we look forward to hearing your feedback at Dynatrace answers or via Dynatrace ONE in-product chat.




Looking for answers?
Start a new discussion or ask for help in our Q&A forum.
Go to forum