
What is Kubernetes security posture management (KSPM)?
Last updated: April 23, 2026
Kubernetes is the go-to container orchestration platform for simultaneously delivering application scalability and agility. But its distributed architecture also introduces significant security challenges. In 2024, misconfigured Kubernetes clusters contributed to 45% of security incidents. Security teams struggle with complex Kubernetes attack surfaces and meeting compliance requirements with traditional monitoring tools, which fail to provide the visibility and agility needed to protect workloads at scale. Kubernetes Security Posture Management (KSPM) comes into play to address these challenges and secure Kubernetes workloads without slowing down development.
What is Kubernetes Security Posture Management (KSPM)?
Kubernetes Security Posture Management (KSPM) is a framework of tools and practices that continuously monitors and secures Kubernetes clusters, and supports adherence to compliance standards. It offers a thorough view of the security posture of Kubernetes resources, enabling organizations to detect and address vulnerabilities and potential threats effectively.
KSPM goes beyond simple configuration management. It offers a strategic approach to assessing, auditing, automating, and remediating security risks associated with Kubernetes deployments.
Key takeaways
Misconfigurations, visibility gaps, and evolving threats make Kubernetes security a moving target. This article will help you:
- Understand KSPM: Learn what it is, how it works, and why traditional security monitoring tools and static scans fall short.
- Recognize hidden risks: Discover how Kubernetes misconfigurations can expose your environment to breaches.
- Learn best practices: Get expert recommendations on building a proactive Kubernetes security automation strategy.
- Evaluate KSPM solutions: Understand the key features of a strong KSPM platform to make the right choice.
Why is KSPM important?
Kubernetes environments often comprise tens of thousands to millions of containers, hundreds or thousands of microservices, and complex configurations, especially in large enterprises. Its configurability and scalability provide organizations with agility but also create a large attack surface. In fact, in 2024, 89% of organizations experienced at least one container or Kubernetes security incident.
As misconfigurations are a leading cause of Kubernetes security incidents, it underscores the importance of visibility – because you can’t fix what you don’t know exists. Neglected misconfigurations (such as mismanaged permissions or unsecured API access) can expose sensitive data and invite malicious activity. Without addressing visibility gaps, organizations face an increased risk of breaches, audit failures, and delays in development due to reactive security processes.
KSPM platforms simplify the process of detecting misconfigurations, adapting security to evolving clusters, enforcing compliance, integrating threat detection and remediation, and reducing human error.
What do KSPM platforms do?
KSPM platforms map, monitor, and actively analyze the cluster’s configuration, resources, workloads, and runtime environment for security misconfigurations. KSPM also provides the mechanism for supporting and automating adherence to regulatory compliance standards, such as DORA and GDPR. A KSPM platform can also initiate automatic remediation workflows to mitigate an issue that compromises a cluster’s performance and compliance status. Here’s a closer look at how KSPM tools work:
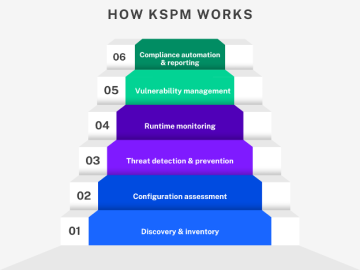
1. Discovery and inventory
First, a KSPM platform ideally identifies all Kubernetes resources including nodes, pods, namespaces, RBAC roles, network policies and configurations. Continuous overview of which components are monitored, and which are not, helps to increase visibility over the potential attack surface and minimizes time spent on manual inventory.
2. Configuration assessment
The platform continuously scans Kubernetes resources, including pods, services, ConfigMaps, secrets, and ingress objects. It evaluates these resources against known best practices (for example: not running containers as root; using namespaces effectively) and compliance standards (such as CIS Benchmarks).
Example: The platform detects if you’ve left a sensitive environment variable in a ConfigMap or secret.
3. Threat detection and prevention
KSPM platforms identify risks, prioritize them based on severity, and offer actionable remediation steps. Some even provide automated remediation capabilities.
Additionally, capabilities that provide anomaly detection to prevent security breaches and respond to incidents can be highly beneficial, especially when integrated with SIEM tools.
Example: The platform recommends applying stricter role-based access control (RBAC) rules for a service account with excessive permissions.
4. Runtime monitoring
Some advanced KSPM platforms use runtime insights to prioritize responses. They observe unauthorized activities or unintentional drift from secure configurations (such as changes to deployments) and prioritize mitigations based on severity.
Example: The platform creates an alert if an unfamiliar image is deployed or if a pod unexpectedly escalates its privileges.
5. Vulnerability management
KSPM platforms scan for vulnerabilities across multiple layers, including container runtimes, language runtimes, and the container orchestrator. They can identify outdated or insecure versions of software at any layer, from application dependencies to Kubernetes components.
Example: The platform flags a container image with an outdated version of nginx or identifies insecure configurations in the container runtime.
6. Compliance automation and reporting
A KSPM platform helps organizations adhere to security and compliance standards. It generates reports to assess cluster compliance posture for frameworks like DORA, CIS Benchmarks, or PCI-DSS. It also offers dashboards and insights to help track compliance and highlight areas needing attention.
Example: A KSPM platform creates a compliance report showing that 80% of assets in your environment meet CIS Kubernetes Benchmark requirements, with specific recommendations to reach 100%.
What is the difference between KSPM and CSPM?
If you’re already familiar with cloud security posture management (CSPM), you might wonder how KSPM compares. Where KSPM focuses on the security posture of Kubernetes environments, CSPM provides automated tools and processes that monitor and manage the security posture of cloud environments as a whole.
Focus area
- CSPM offers visibility into the hybrid cloud and multi-cloud infrastructure, focusing on protecting cloud resources like databases, storage buckets, and virtual machines.
- KSPM focuses specifically on Kubernetes environments, focusing on configurations and runtime monitoring, including clusters, pods, and services.
Why add KSPM to your organization’s cloud security strategy?
KSPM is critical for organizations adopting Kubernetes in production. Here’s why it needs to be integrated into your security approach:
1. Proactively prevent misconfigurations
Misconfigurations account for a large percentage of cloud security breaches. KSPM identifies these issues before they escalate, enabling teams to take preventive action.
2. Improve visibility across clusters
Without a holistic view of your Kubernetes clusters, it’s nearly impossible to manage and enforce security effectively. With the ability to deal with the scale of Kubernetes, KSPM provides centralized visibility, even for sprawling, multi-cluster environments.
3. Cost efficiency
Detecting and addressing vulnerabilities early not only saves time but also prevents costly breaches and downtime. KSPM automates security checks and remediation, reducing manual overhead for DevOps and security teams while improving security posture. Implementing continuous compliance enforcement also decreases costs you might otherwise spend on the third-party audit preparations.
4. Streamline compliance processes
With regulatory compliance becoming a growing concern, KSPM helps automate aspects of meeting regulatory standards. Teams can use KSPM to enforce internally set compliance requirements that prescriptively meet a regulation’s external requirements. Teams can use KSPM to enforce security measures and controls as part of their legal and regulatory compliance efforts to help meet legal and regulatory obligations. The structure and automation of a KSPM solution makes audits smoother and helps organizations stay compliant 24/7.
5. Enhance team collaboration
By integrating KSPM into CI/CD pipelines, teams can work together more effectively. Development, DevOps, SRE, security, and compliance teams can address vulnerabilities and compliance gaps, ensuring smoother builds and deployments.
What to look for in a KSPM solution
Many KSPM tools offer configuration scanning, but few provide runtime AI-powered risk prioritization and deep observability context to reduce alert fatigue. The best KSPM solutions integrate seamlessly with CI/CD pipelines and existing IT Ops tooling and security workflows, reducing manual effort while enabling compliance at scale.
When choosing a KSPM platform, ensure it meets the following essential criteria:
- Broad support for benchmark and compliance standards: A KSPM solution should support widely accepted security benchmarks like CIS Kubernetes Benchmark and regulatory standards, but also offer customizable policies for unique use cases.
- Ease of integration: Look for a solution that integrates seamlessly with your CI/CD pipeline, observability and security solutions, and existing cloud infrastructure.
- Observability/runtime context: A KSPM solution should provide runtime security checks and prioritize remediation based on impact.
- Multi-cluster and multi-cloud support: If your organization operates across multiple clusters or cloud providers, the KSPM platform should cater to heterogenous environments to provide a unified view.
- Real-time monitoring: Ensure the solution offers runtime protection and alerts for real-time threats, such as unauthorized access or privilege escalations.
- Flexible, detailed reporting: A good KSPM platform not only provides comprehensive reporting on vulnerabilities, misconfigurations, and compliance status—making it easier for teams to act quickly and document results—but also provides context relevant for management and business.
KSPM best practices
The following are some practical tips to maximize the effectiveness of your Kubernetes security posture management strategy.
- Conduct regular security audits: Schedule frequent, automated audits of your Kubernetes clusters using your KSPM solution to catch and fix misconfigurations on time.
- Establish a baseline before you enforce: Before enabling automated remediation, run KSPM in observation mode to understand your environment's "normal." Jumping straight to enforcement without a baseline can cause disruption and erode team trust in the tool.
- Prioritize remediation by blast radius, not just severity: A critical misconfiguration in an isolated dev namespace is less urgent than a medium-severity one in a cluster running customer-facing workloads. Contextualize risk by what's actually exposed.
- Enforce role-based access control (RBAC): Role-based access control (RBAC) is essential to ensure that only authorized users can access and manage your KSPM solution. While KSPM is not responsible for enforcing RBAC across your entire cloud environment, it should have RBAC controls in place to protect its own data, helping to prevent misuse and privilege escalation.
- Integrate KSPM checks with CI/CD workflows: Ensure that KSPM checks (such as container image scans) are embedded into your CI/CD pipeline so you can spot misconfigurations and vulnerabilities early in the software development lifecycle.
Safeguarding Kubernetes with KSPM
Misconfigurations are one of the top threats to Kubernetes environments, and they can compromise your organization’s security posture in seconds. For CISOs and business leaders focused on protecting critical infrastructure, staying ahead of these vulnerabilities is paramount.
Safeguarding Kubernetes with an observability platform that provides KSPM as part of a comprehensive observability strategy is a smart, efficient way to establish robust security and compliance. By easily assessing deployments against required standards, a platform-based KSPM solution can deliver actionable insights that help prevent potential compliance and configuration issues and help teams see context beyond just KSPM findings.
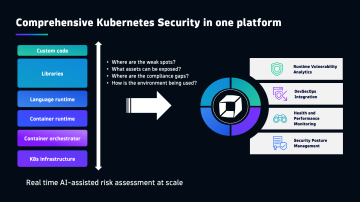
A KSPM solution that provides AI-driven prioritization, built-in guidance, and automated workflows enables rapid remediation of misconfigurations and vulnerabilities.
Additionally, a solution like Dynatrace that’s based on deep observability and seamless security integration offers comprehensive visibility, empowering your organization with the actionable insights you need to maintain a secure and compliant Kubernetes environment.
FAQs about KSPM
How does KSPM identify and help remediate security misconfigurations?
KSPM platforms continuously scan Kubernetes resources, including pods, services, and network policies, deployments, and RBAC policies against known best practices and compliance standards, such as CIS Benchmarks or DORA. They detect issues like insecure environment variables, publicly exposed services, or overly permissive access controls. Once identified, KSPM helps prioritize risks based on severity, exploitability and potential impact, and offers actionable remediation steps, such as configuration changes or policy updates. Some solutions can also trigger automated workflows (e.g., via Infrastructure as Code pipelines or ticketing integrations) to mitigate problems and restore compliance.
What types of misconfigurations does Kubernetes Security Posture Management (KSPM) address?
KSPM primarily addresses misconfigurations within Kubernetes clusters, which are a major source of infrastructure security incidents. These include misconfigured RBAC roles and bindings, lack of network segmentation, disabled audit logging, exposed dashboards, insecure workload settings (e.g., privileged containers, hostPath mounts), and missing resource limits.
It may also identify configuration-related risks in supporting components such as etcd, kube-apiserver, and kubelet, as well as flag outdated Kubernetes versions that no longer receive security patches. Additionally, KSPM can flag issues related to access control and excessive permissions, helping to reduce the attack surface.
Why is integrating KSPM into CI/CD pipelines considered a best practice?
Integrating KSPM into CI/CD pipelines allows for the early detection of misconfigurations and vulnerabilities within the software development lifecycle. This "shift-left" approach enables development, DevOps, and security teams to address potential issues proactively before they reach production. Embedding KSPM checks ensures that security is an inherent part of continuous integration and delivery, preventing insecure configurations from being deployed to clusters in the first place, leading to smoother builds and deployments while maintaining a strong security posture.
How does KSPM contribute to an organization's compliance efforts?
KSPM automates the enforcement of security measures and controls, which is crucial for supporting efforts to meet legal and regulatory obligations. It helps organizations adhere to security and compliance standards by continuously assessing cluster posture against frameworks like DORA, CIS Benchmarks, or PCI-DSS. This automation simplifies audit preparations by providing continuous evidence collection, policy mapping to control requirements, historical posture tracking, and exportable compliance reports. As a result, organizations reduce manual overhead and maintain ongoing visibility into their compliance status rather than relying solely on point-in-time audits.


